

The Perytons™ Protocol Analyzers support analysis of encrypted messages as well as re-encryption of messages (valid only if the Peryton-Traffic Generator Add-On is installed – see chapter V.1).
Deciphering secured messages is possible if the required information is known to the Perytons™ Protocol Analyzer. This information includes keys, as well as additional information (e.g. security level and long mac address if not included in the message).
The Perytons™ Protocol Analyzer supports the following protocol layers security schemes:
•IEEE 802.15.4 MAC
•ZigBee NWL
•ZigBee APS
•ZigBee RF4CE
•ZigBee Green Power
Security may be based on a single known key (i.e. Master Key), on a per-Network Key, or on a link key shared by any two devices.
The known security keys should be placed in the security keys table info by using the Security option in the Tools menu or when pressing the relevant icon in the Main Window Menu:
Figure 252 – Security Tool Menu
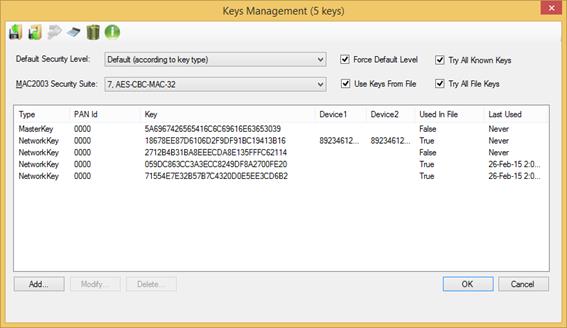
Figure 253 – Security Keys List form
Perytons™ security processing
parameters can be set either through this form or through the User Preferences –
Processing Tab (See paragraph 19.8 for details). Setting through one of these
two methods is sufficient.
Note: If after the initial Keys entered
there is an interchange of Keys between devices and a new Key is created for
use, the Perytons™ Protocol Analyzer will 'catch' the new Security Key 'On the
Fly' and will automatically keep record of it and add it to the Keys List for
use as an additional key.
This process is especially useful for protocol
sessions that involve generation of new Link Keys based on a basic initial
Security Key.