When processing an encrypted message, the Perytons™ Protocol Analyzer looks for the relevant key given message parameters (e.g. key type, sequence number, source and destination addresses etc.).
However, in some cases, the Network Keys table may have ambiguity regarding the key that should be used. For example if the user entered several different Network Keys for the same PAN address with the same sequence number. In such case the analyzer will use the last key in the list which is not necessarily the key needed.
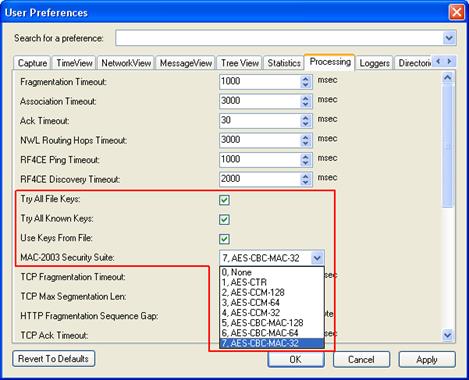
The Processing section in the Preferences form includes security settings that allow the user to set the encryption algorithm used and to let the analyzer try multiple keys from the list until the message is well deciphered:
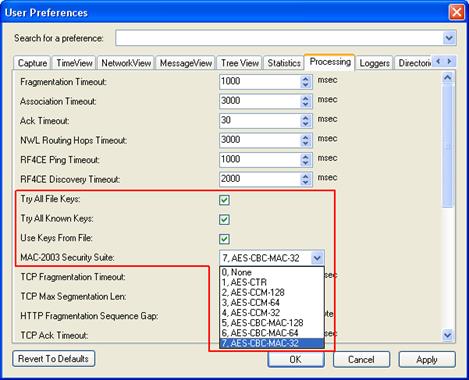
Figure 261 – Security Preferences Settings
Note: Trying multiple Keys increases the processing time, and is not recommended to be used during real time capture if the keys list includes more than 5-10 keys (depending on the PC capabilities).See par. 19.8.