Holds parameters related to protocol processing:
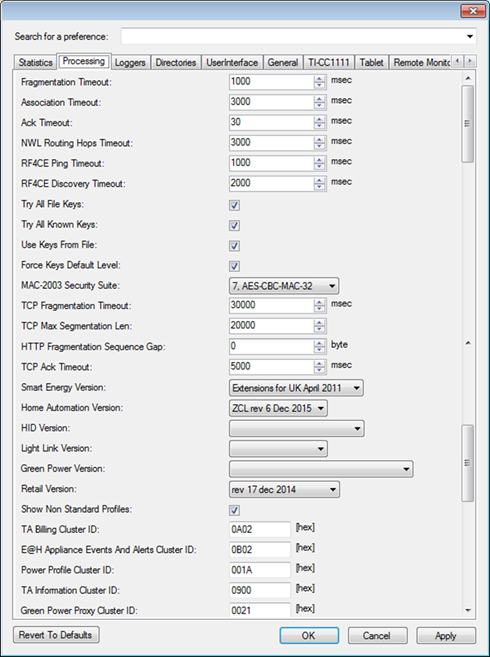
Figure 298 – Preferences, Processing tab – Top section
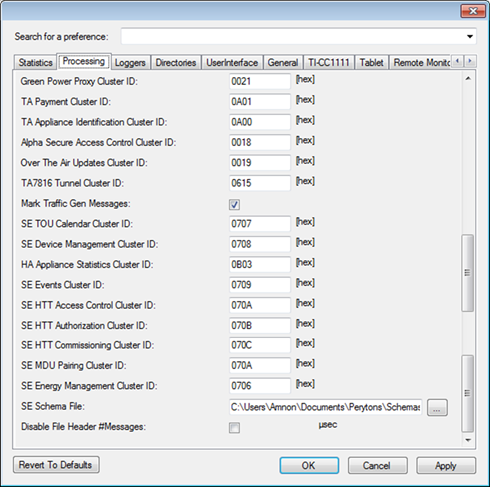
Figure 299 – Preferences, Processing tab – Bottom section
•Fragmentation Timeout:
Time in milliseconds from receiving the first fragment until the de-fragmentation process drops the message. This parameter is usually defined by the protocol documentation.
•Association Timeout:
Maximal time in milliseconds that the analyzer will 'look back' checking for association request for the association reply that was just received.
•Ack Timeout:
Maximal time in milliseconds that the analyzer will 'wait' for an acknowledgement of a message and still refer to it as an acknowledgement.
•NWL Routing Hops Timeout:
Maximal time in milliseconds that the analyzer will 'look back' and check for Network Layer Routing Hops messages and still refer to it as a NWL Routing message.
•RF4CE Ping Timeout:
Maximal time in milliseconds allowed for an RF4CE Ping request and until a Ping respond is received. After this time, the Ping response will not be associated to the initial Ping request.
•RF4CE Discovery Timeout:
Maximal time in milliseconds to allow for the RF4CE discovery process.
•Try All File Keys:, Try All Known Keys: and Use Keys From File
Set which keys to process. See par. 0.
•Force Keys Default Level: The user can force using the Default Key Level regardless of the Key Level set individually for each encryption key. This is accomplished by selecting the ‘Force Default Level’ checkbox (unless there is a specific different need, having ‘Force Default Level’ checkbox selected is recommended).
•MAC-2003 Security Suite:
If the user is interested to use deciphering algorithms based on the MAC-2003 Security Suite, he can choose the deciphering algorithm to use from the drop-down list:
o 0. None – Do not use the MAC-2003 Security Suite
o 1. AES-CTR
o 2. AES-CCM-128
o 3. AES-CCM-64
o 4. AES-CCM-32
o 5. AES-CBC-MAC-128
o 6. AES-CBC-MAC-64
o 7. AES-CBC-MAC-32
Notes:
MAC2003 Security
Suite type can be set either through this form or through the Security section
(See chapter 16 for
details). Setting through one of these two methods is sufficient.
Unlike the
plain Master key level (when MAC2003 Security Suite is set to '0. None'), levels
1 to 7 of the MAC2003 Security Key are not included in the data capture (.ANL)
file. In such case in order to decipher the data of a given data capture file,
the user needs to set the key manually.
When choosing MAC2003 level '1. AES
CTR', the 'Try All Keys' option is ignored.
•TCP Fragmentation Timeout:
Unlike other protocols, TCP messages
can be take quite a long time from the first message of a fragment is received
and until the last message of the fragment is received (and in-between different
fragments might be received asynchronously and without following the fragments'
series order).
This variable sets the time in milliseconds from receiving the
first TCP message fragment until the last fragment of the series is expected
until the de-fragmentation process drops the message and sets a relevant
error.
•TCP Max Segmentation Len:
This variable sets the maximal length of a full (de-fragmented) TCP message in number of received characters.
•HTTP Fragmentation Sequence Gap:
Max HTTP fragmentation sequence gap. When the sequence number of a new fragment exceeds this gap (from the end of the previous fragment), the old fragments are discarded.
•TCP Ack Timeout:
Maximal time in milliseconds that the analyzer will 'wait' for an acknowledgement of a TCP message and still refer to it as an acknowledgement.
•Smart Energy Version:
The user can choose between different Smart Energy profile versions when analyzing ZigBee Smart Energy V1.x based networks:
o 1.0 rev. 15
o 1.0 Jan. 2010
o 1.1 ver. 09
o 1.1 r18 October 7 2012
o Extensions for UK April 2011
o 1.2 Dec 2012
o 1.2 Aug 2013
•Home Automation Version:
The user can choose between different HA (Human Interface Devices) profile versions when analyzing ZigBee HA based networks:
o before 1.2 rev 29
o 1.2 rev 29
•HID Version:
The user can choose between different HID (Human Interface Devices) profile versions when analyzing ZigBee HID based networks:
o rev. 08 August 2010
o rev 10 Jan. 2011
o rev 10 March 8 2011
o GDP March 2011
o June 2011 (HID r15, GDP r1)
o January 2013
o 2.0 Feb 2014
•Light Link Version:
The user can choose between different LL (Light Link) profile versions when analyzing ZigBee LL based networks:
o 1.0 rev 10
o 1.1 rev 02
•Show Non Standard Profiles:
When checked the analyzer will analyze known clusters although the profile might be unknown (i.e. vendor specific or not released yet).
•TA Billing Cluster ID:
The user can change here the Telecom Services (AKA Telecom applications) Cluster ID in hex – to avoid Cluster ID conflicts
•E@H Appliance Events and Alerts Cluster ID:
The user can change here the Energy at Home Events and Alerts Cluster ID in hex – to avoid Cluster ID conflicts
•Power Profile Cluster ID:
The user can change here the Power Profile Cluster ID in hex – to avoid Cluster ID conflicts
•TA Information Cluster ID:
The user can change here the Telecom Services (AKA Telecom applications) Information Cluster ID in hex – to avoid Cluster ID conflicts
•Green Power Proxy Cluster ID:
The user can change here the Green Power Proxy Cluster ID in hex – to avoid Cluster ID conflicts
•TA Payment Cluster ID:
The user can change here the Telecom Services (AKA Telecom applications) Payment Cluster ID in hex – to avoid Cluster ID conflicts
•TA Appliance Identification Cluster ID:
The user can change here the Telecom Services (AKA Telecom applications) Appliance Identification Cluster ID in hex – to avoid Cluster ID conflicts
•Alpha Secure Access Control Cluster ID:
The user can change here the Alpha Secure Access Control Cluster ID in hex – to avoid Cluster ID conflicts
•Over The Air Updates Cluster ID:
The user can change here the Over The Air Updates Cluster ID in hex – to avoid Cluster ID conflicts
•TA7816 Tunnel Cluster ID:
The user can change here the TA7816 Tunnel Cluster ID in hex – to avoid Cluster ID conflicts
•Mark Traffic Gen Messages: - valid only when the Peryton-TG Add-On is installed
Mark Traffic-Generated messages from the same Perytons™ Protocol Analyzer especially to allow easy differentiation between them and messages captured through the front-end device/s.
•SE TOU Calendar Cluster ID:
The user can change here the SE TOU Calendar Cluster ID in hex – to avoid Cluster ID conflicts
•SE Device Management Cluster ID:
The user can change here the SE Device Management Cluster ID in hex – to avoid Cluster ID conflicts
•HA Appliance Statistics Cluster ID:
The user can change here the HA Appliance Statistics Cluster ID in hex – to avoid Cluster ID conflicts
•SE Events Cluster ID:
The user can change here the SE Events Cluster ID in hex – to avoid Cluster ID conflicts
•SE HTT Access Control Cluster ID:
The user can change here the SE HTT Access Control Cluster ID in hex – to avoid Cluster ID conflicts
•SE HTT Authorization Cluster ID:
The user can change here the SE HTT Authorization Cluster ID in hex – to avoid Cluster ID conflicts
•SE HTT Commissioning Cluster ID:
The user can change here the SE HTT Commissioning Cluster ID in hex – to avoid Cluster ID conflicts
•SE MDU Pairing Cluster ID:
The user can change here the SE MDU Pairing Cluster ID in hex – to avoid Cluster ID conflicts
•SE Energy Management Cluster ID:
The user can change here the SE Energy Management Cluster ID in hex – to avoid Cluster ID conflicts
•SE Schema File:
The user should set here the specific Schema File name that is used to de-compress EXI compressed payload